network
Citrix CVAD and MTU Discovery
Update November 2022:
Martin Latteier wrote me that Citrix introduces a new feature which addresses the issue. Fact is, on certain cable connections with DS-Lite (IPv6 only) the MTU discovery with EDT did not work properly, because the cable modem did not process the “DF flag”, which caused the MTU discovery to detect a too high MTU, the datagrams had to be fragmented and the performance was bad. The solution was to switch off EDT on the client side or to change the MTU discovery to a static MTU (edtMSS=13xx).
If you set this flag the issue should be solved:

Update January 2022:
Only update the default.ica how it’s described below, referencing to https://support.citrix.com/article/CTX231821 if you also are using Citrix Workspace App for Mac in Version 2201 or later!
Recently I saw an increased number of issues by connecting to Citrix virtual desktops and apps. Desktops were connected from private devices over a Citrix ADC (aka Netscaler) but virtual apps were connected from our internal network from different branch offices.
I wrote a blog article some weeks ago: Issues by accessing Citrix Virtual Apps and Desktops on a pure IPv6 Internet Provider with enabled EDT
Our first workaround for this issue was to disable the UDP based EDT protocol which is now the default for Citrix Virtual Apps and Desktops. But this is not really our intended solution because all the benefits of EDT get lost, so we just did it on client-side with a reg hack, but so we have to identify all the clients with issues. (see the recent blog article)
Further analysis of this issue showed that the root cause of this issue is on the MTU, which means the Maximum Transmission Unit or simplified said Package size.
I found out that our branch offices has a smaller MTU than 1500 what is the default, the reason is a crypto-tunnel which is configured to all our branches. So there will be a fragmentation of the packages, in some cases the fragmentation causes problems because the payload is no more enough that a session launch will work. It looks like EDT is much more sensible on that than the classic ICA protocol on TCP.
Solution 1: How to configure MSS when using EDT on networks with non-standard MTU
In the recent blog article, I called Citrix “please fix that” but they already started on this at this point. In this article, you can see how to configure EDT for non-standard MTUs https://support.citrix.com/article/CTX231821 e.g. put the MTU to 1480 with the default.ica
The disadvantage of this solution is that the MTU is lowered for all connections, also it’s needed to figure out which MTU fits best. The benefit of this solution that it works on every platform with the exception of Android.
Solution 2: enable MTU Discovery
An even smarter option Citrix introduces on the background with CVAD 19.12, this is MTU Discovery for EDT. This feature gives the possibility to have the best MTU for each session. MTU discovery is not a invention by Citrix, just new on EDT. You can read more about MTU discovery here:
https://en.wikipedia.org/wiki/Path_MTU_Discovery
I tried to visualize these 3 scenarios:
standard, MTU set to 1500

The default is that MTU of 1500 bytes are sent, if the MTU on the path is somewhere smaller the package gets fragmented, what is not a big issue but in real life we see that it can be a problem.
MTU reduced to 1380 bytes according to the mentioned Citrix article
(Change in default.ica on StoreFront)

Now packaged of 1380 bytes are transmitted.
– Is the possible MTU somewhere on the path smaller than 1380, the packages are still fragmented. Example on this picture, the BYOD client from the Internet.
– Also, the MTU is lowered when not needed, in this example the Client in the HQ
+ This solution works on all platforms except Android.
MTU with MTU Discovery (Registry Setting on VDA)

+ The MTU is figured out optimal and individually for every session. First, the Session will start with 1024 bytes and the MTU will be increased during the Session.
– Needs Citrix Workspace App for Windows 19.11 or newer.
– If the connection goes over an ADC its a minimum required version 13.0.52.24 or 12.1.56.22. If you are on a lower version the MTU perhaps remains on 1024 bytes!
You can check your EDT MTU with this command:
ctxsession -v

MTU Discovery is today not active as a default, you need to activate it on the VDA with a Registry Key, the VDA must be at minimum 19.12, details here: https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/technical-overview/hdx/adaptive-transport.html#edt-mtu-discovery
Update 5.6.2020 – Combine solutions 1 and 2 and have the best config!
For our case, we have separated Storefront Servers for access via ADC, so I decided to implement a solution with the best of both worlds… I set the MTU in the default.ica to 1300 and I enable MTU Discovery – so Apple macOS can use the setting from the default.ica and Windows computers have the optimal value with MTU discovery
Technical:
on VDA, add this DWORD: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\Wds\icawd
Name: MtuDiscovery
Type: DWORD
Data: 00000001
default.ica, add this lines:
OutBufLength=1300
udtMSS=1300
edtMSS=1300

If MTU Discovery is active, means enabled and accessed from a Citrix Workplace App the MTU Discovery override the value set in the default.ica, what is very helpful!
How do you configure MTU on your Citrix with EDT environment? Leave a comment!
How to bring your network back online in minutes with Ubiquiti UniFi gear
Less than a month ago I decided to buy a new WiFi Access Point to increase the quality and possibilities of my Home Wifi. Until now I just had a “Fritzbox” which is already very nice for home use. Fritz does anything, Fast WiFi, Modem, Router, VoIP, Call answer machine, DECT Gateway and it’s stable and easy to configure. Of course, I wished to have a more enterprise-like network setup, especially because also my lab environment is in my home network and a lot of IoT stuff. But honestly the components I had known that allows enterprise features were not in my budget.
So the first plan was to just increase WiFi. I just bought a Ubiquiti UniFi AP-AC-Pro without any ulterior motive. But to be honest, the new AP was like a starter drug. I saw what all is possible and for a price which is also payable for home use and with no extra license costs. I don’t want to write a review here about my new awesome Ubiquiti gear if you wish to know more about that stuff see here the blog post from my fellow CTP Jason Samuel: Building a secure high visibility WiFi network using Ubiquiti Networks UniFi gear
Just to say, now, some weeks later I have a Router (UniFi Security Gateway 3P), a managed Switch (UniFi Switch 16 POE-150W) and two WiFi AccessPoints (UniFi AP-AC-Pro and UniFi AP-AC-LR) in my Network from Ubiquiti. Finally, I’m able to segment my home network in virtual networks (VLANs) and to make all more transparent, hopefully, more secure and of course easier to manage for me. Currently, I have 3 different WiFi SSIDs and 4 VLANs. The software-defined network is great and let me do things I just dreamed of before. When I think about all the “use cases” I’m now really sure that a lot of Security considerations should be made for improvements in the network segment should be done … but that’s another topic …
The USG 3P, UniFi Security Gateway comes with 3 Ports, WAN, LAN, and VoIP. The Software of these devices will be always further developed and new features come with every new version. Some features are also implemented as beta features, e.g also to make out of the VoIP a WAN2 port:

 With this feature, it’s possible to have a Second WAN link and to use it as Failover or as Weighted LB. Of course for home use, a second WAN link is not common. But definitely interesting for some small companies or maybe branch offices which need a reliable connection to the internet.
With this feature, it’s possible to have a Second WAN link and to use it as Failover or as Weighted LB. Of course for home use, a second WAN link is not common. But definitely interesting for some small companies or maybe branch offices which need a reliable connection to the internet.
I have currently only one connection to the Internet, a cable connection with 250M down and 25M up from “Quickline”. Until now when I had an outage I was still able to use my 4G WiFi Hotspot from Huawei to access the Internet with my Laptop.
 Last Saturday my Cable Internet connection was interrupted exactly at that moment where I was doing some lab works with my network components. So I decided to have a closer look at this WAN 2 Feature. I connected a Zyxel travel router (NBG2105) with the Cat5 cable to the USG and with WLAN to my 4G WiFi router, I configured the VoIP Port for WAN2. Wow after 30 minutes I was back online with my whole network.
Last Saturday my Cable Internet connection was interrupted exactly at that moment where I was doing some lab works with my network components. So I decided to have a closer look at this WAN 2 Feature. I connected a Zyxel travel router (NBG2105) with the Cat5 cable to the USG and with WLAN to my 4G WiFi router, I configured the VoIP Port for WAN2. Wow after 30 minutes I was back online with my whole network.

On WAN2 there can just be anything that is providing an Internet link and give an IP address via DHCP in my case. Of course, first I connected the Zyxel NBG2105 with the cable to my laptop and connected with it to my WiFi router. The most important thing here with the NBG2105 is that the Switch is set to Client:

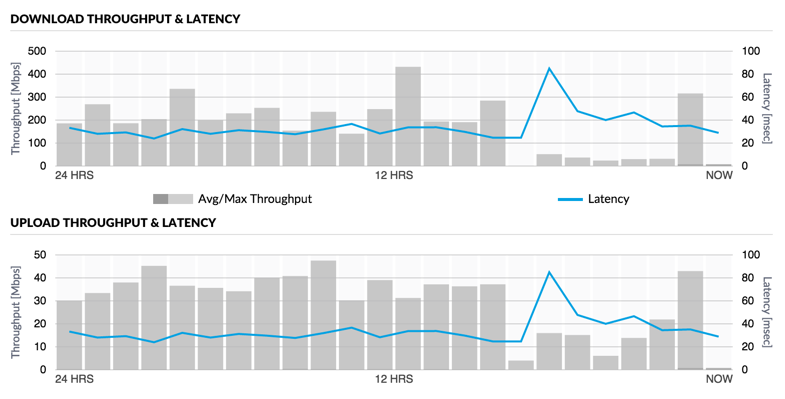
Of course the Speed of 4G is not near my cable connection but it’s still better than be offline:
And now I have not just the solution to “How to get back online” but rather also to “Stay always online”.

