Customizing
Citrix CVAD and MTU Discovery
Update November 2022:
Martin Latteier wrote me that Citrix introduces a new feature which addresses the issue. Fact is, on certain cable connections with DS-Lite (IPv6 only) the MTU discovery with EDT did not work properly, because the cable modem did not process the “DF flag”, which caused the MTU discovery to detect a too high MTU, the datagrams had to be fragmented and the performance was bad. The solution was to switch off EDT on the client side or to change the MTU discovery to a static MTU (edtMSS=13xx).
If you set this flag the issue should be solved:

Update January 2022:
Only update the default.ica how it’s described below, referencing to https://support.citrix.com/article/CTX231821 if you also are using Citrix Workspace App for Mac in Version 2201 or later!
Recently I saw an increased number of issues by connecting to Citrix virtual desktops and apps. Desktops were connected from private devices over a Citrix ADC (aka Netscaler) but virtual apps were connected from our internal network from different branch offices.
I wrote a blog article some weeks ago: Issues by accessing Citrix Virtual Apps and Desktops on a pure IPv6 Internet Provider with enabled EDT
Our first workaround for this issue was to disable the UDP based EDT protocol which is now the default for Citrix Virtual Apps and Desktops. But this is not really our intended solution because all the benefits of EDT get lost, so we just did it on client-side with a reg hack, but so we have to identify all the clients with issues. (see the recent blog article)
Further analysis of this issue showed that the root cause of this issue is on the MTU, which means the Maximum Transmission Unit or simplified said Package size.
I found out that our branch offices has a smaller MTU than 1500 what is the default, the reason is a crypto-tunnel which is configured to all our branches. So there will be a fragmentation of the packages, in some cases the fragmentation causes problems because the payload is no more enough that a session launch will work. It looks like EDT is much more sensible on that than the classic ICA protocol on TCP.
Solution 1: How to configure MSS when using EDT on networks with non-standard MTU
In the recent blog article, I called Citrix “please fix that” but they already started on this at this point. In this article, you can see how to configure EDT for non-standard MTUs https://support.citrix.com/article/CTX231821 e.g. put the MTU to 1480 with the default.ica
The disadvantage of this solution is that the MTU is lowered for all connections, also it’s needed to figure out which MTU fits best. The benefit of this solution that it works on every platform with the exception of Android.
Solution 2: enable MTU Discovery
An even smarter option Citrix introduces on the background with CVAD 19.12, this is MTU Discovery for EDT. This feature gives the possibility to have the best MTU for each session. MTU discovery is not a invention by Citrix, just new on EDT. You can read more about MTU discovery here:
https://en.wikipedia.org/wiki/Path_MTU_Discovery
I tried to visualize these 3 scenarios:
standard, MTU set to 1500

The default is that MTU of 1500 bytes are sent, if the MTU on the path is somewhere smaller the package gets fragmented, what is not a big issue but in real life we see that it can be a problem.
MTU reduced to 1380 bytes according to the mentioned Citrix article
(Change in default.ica on StoreFront)

Now packaged of 1380 bytes are transmitted.
– Is the possible MTU somewhere on the path smaller than 1380, the packages are still fragmented. Example on this picture, the BYOD client from the Internet.
– Also, the MTU is lowered when not needed, in this example the Client in the HQ
+ This solution works on all platforms except Android.
MTU with MTU Discovery (Registry Setting on VDA)

+ The MTU is figured out optimal and individually for every session. First, the Session will start with 1024 bytes and the MTU will be increased during the Session.
– Needs Citrix Workspace App for Windows 19.11 or newer.
– If the connection goes over an ADC its a minimum required version 13.0.52.24 or 12.1.56.22. If you are on a lower version the MTU perhaps remains on 1024 bytes!
You can check your EDT MTU with this command:
ctxsession -v

MTU Discovery is today not active as a default, you need to activate it on the VDA with a Registry Key, the VDA must be at minimum 19.12, details here: https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/technical-overview/hdx/adaptive-transport.html#edt-mtu-discovery
Update 5.6.2020 – Combine solutions 1 and 2 and have the best config!
For our case, we have separated Storefront Servers for access via ADC, so I decided to implement a solution with the best of both worlds… I set the MTU in the default.ica to 1300 and I enable MTU Discovery – so Apple macOS can use the setting from the default.ica and Windows computers have the optimal value with MTU discovery
Technical:
on VDA, add this DWORD: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\Wds\icawd
Name: MtuDiscovery
Type: DWORD
Data: 00000001
default.ica, add this lines:
OutBufLength=1300
udtMSS=1300
edtMSS=1300

If MTU Discovery is active, means enabled and accessed from a Citrix Workplace App the MTU Discovery override the value set in the default.ica, what is very helpful!
How do you configure MTU on your Citrix with EDT environment? Leave a comment!
StoreFront – Allow relogin without browser close
Citrix StoreFront is able to handle Logins with SmartCards, and after a successful SmartCard Login you cannot Logoff and Login again before you close the Browser, you will see this message:

You have logged off successfully. Please close your browser to protect your account.
According the message, this is a feature and not a bug … Not in every case a Re-Login is a security problem as for example if SmartCards are mandatory in general you need to logon also on the VDI or the application with your SmartCard.
Especially as an Admin working with multiple accounts it can be very annoying.
In scope of the CTP program I’ve asked Citrix to improve that and give Citrix admins the possibility to configure this security feature in future versions. Now when StoreFront 3.8 was released I complained that this is still not implemented.
Feng Huang then gave me the hint that this is actually configurable but not yet implemented into the GUI.
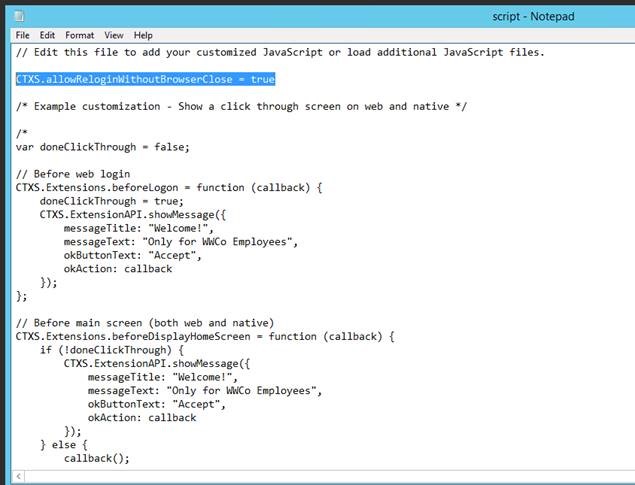
All what must be done is to add the line CTXS.allowReloginWithoutBrowserClose = true in the file C:\inetpub\wwwroot\Citrix\YOURSTORE\custom\script.js
THANKS Citrix for Listening to special requests!
Display the server name on Citrix StoreFront 2.0 WebReceiver
In enterprise environments most admins have more than one Citrix Storefront Webserver and loadbalance them over a Netscaler, F5 or something equivalent.If a user has a misbehaviour on the website it’s not always easy to find out on which Storefront Website this user is working. To simplify troubleshooting it can be helpful to know which web server user is accessing.
To see this on the website just add the following lines to the bold written files:
C:\inetpub\wwwroot\Citrix\[Storenname]\contrib\custom.style.css
#SFserver {
padding-right: 30px;
padding-bottom: 20px;
float: right;
color: silver;
}
$(document).ready(function() {
var $markup = $('<div id="SFserver">Storefront: [Name of the Server e.g. StoreFront001] </div>');
$('#resources-footer').append($markup);
});
This can also be done dynamic with JavaScript (System.Environment.machineName) but I had some troubles with formatting … and maybe you wont reveal the real hostname and just put an alias there to distinguish on which server the user is working.
Keep in mind that this file will be updated/overwritten in a multi server environment when you click on propagate changes.
By the way, if you need this for the legacy Citrix Webinterface visit: http://techblog.deptive.co.nz/2012/03/display-server-name-on-citrix-web.html


