Surface Arc Mouse on iPhone with Windows App — and how to stop your screen from falling asleep mid-session
Picture this: the room you normally use as your home office doubles as the guest bedroom, and right now your guest is fast asleep in there at 7am. But you still need to work. So you grab your iPhone, your Surface Arc Mouse, your Logitech K830 keyboard, fire up the Windows App, mirror everything to the living room TV via AirPlay, and suddenly you have a fully functional Windows desktop from the couch. No laptop needed.
This was my setup this morning. I got my Surface Arc Mouse yesterday, played around with this setup, and already ran into the firmware update process. It works surprisingly well, once you figure out the sleep problem.
Part 1 — Surface mouse on iOS: it’s a preview, but it works
Microsoft quietly added Surface mouse support to the Windows App on iOS. It’s currently in preview, and only specific devices and firmware versions are supported. Let’s go through the setup.
Supported devices
- Surface Mouse
- Surface Arc Mouse
Prerequisites
- iPhone 15 or above with Bluetooth enabled
- A Windows PC with the latest Windows updates installed
- A supported Surface mouse
Step 1 — Firmware update (don’t skip this)
Before anything works, your mouse needs a firmware update. And here’s where Apple fans get a gentle reminder that the world does not always revolve around them — the firmware update can only be done from a Windows PC. Not iPhone. Not iPad. Windows. You’ve been warned.
The required firmware versions and download links for both the Surface Mouse and Surface Arc Mouse are listed in the Microsoft documentation. Run the MSI package in administrator mode on a Windows PC, connect the mouse via Bluetooth, and leave it sitting there for 10 minutes doing absolutely nothing. (Yes, really. Ten minutes. Firmware is not in a hurry.)
Step 2 — Pair with iPhone
Settings → Bluetooth → select the mouse from the list of available devices.Step 3 — Use it in the Windows App
Open the Windows App, start your AVD or Cloud PC session — the mouse is automatically detected. No additional configuration required. You’ll see a proper Windows cursor in your remote session. It genuinely feels like sitting at a desk.
Part 2 — The problem: your iPhone falls asleep
Here’s the catch nobody tells you about. When you’re using a physical mouse and keyboard with your remote session, you’re not touching the iPhone screen. And iOS, in its infinite wisdom, sees zero screen activity — so after your Auto-Lock timeout, the screen dims and locks.
Your AVD session is still alive on the server. But you’re looking at a lock screen. Every. Few. Minutes.
The good news: there are several ways to deal with this. SimplyMac has a solid overview of all options: How to Keep an iPhone from Sleeping. Here are the most practical ones for our AVD use case:
Option A — Move the mouse?
Really, constantly moving the mouse and don’t stop it for more than 30 sec. Guess not …
Option B — Extend Auto-Lock to never or the possible maximum
By default, iOS locks the screen after 30 seconds of inactivity. You can extend this to never or up to the maximum your company has defined if you have an MDM managed device, in my case 5 minutes under Settings > Display & Brightness > Auto-Lock. That buys you more breathing room between interactions, though it does not fully solve the problem for longer sessions where you are heads-down in your remote desktop.
Security note: The longer your Auto-Lock timeout, the longer your phone stays unlocked and accessible if you step away or leave it unattended. In a home setup this is usually fine, but keep it in mind, especially in shared or public spaces.
Option C — Guided Access
iOS Accessibility feature that locks the phone into a single app and can prevent the screen from sleeping. Enable under Settings → Accessibility → Guided Access, then triple-click the side button when the Windows App is open. Slightly more setup, but reliable for longer sessions.
Option D — iOS Shortcuts automation (advanced)
For those who want it fully automatic: you can build a Shortcuts automation that sets Auto-Lock to “the maximum value” when the Windows App opens, and restores your normal setting when it closes. iOS Shortcuts supports app-open and app-close triggers — a neat two-automation setup if you’re comfortable with the Shortcuts app.
Hey Microsoft — one more thing
Until then: mouse around, pick your workaround of choice, and enjoy your living room office setup. The sleeping guest is optional but a good reason to show off with this use case…
Microsoft Teams for Mac on AVD & Windows 365: SlimCore Optimization is Now in Public Preview
If you know me, you know: I’ve been using Mac in my personal life since 2006. Not because I’m an Apple fanboy, but simply because it’s the better tool for me. And if you’re familiar with the EUC world, you also know that hasn’t always been straightforward. macOS has traditionally received new features a little later than Windows. With solutions like Microsoft Azure Virtual Desktop (AVD) or Windows 365, accessing corporate environments from a Mac has become quite solid, and here too, things have improved massively over the last few months.
But when it comes to Microsoft Teams in a VDI environment, Mac users like me have been at a slight disadvantage in recent months. On Windows, Teams optimization with AVD has worked reliably for years. On Mac, however, you were stuck with the older WebRTC-based optimization, missing out on features that Windows users had long enjoyed. That is now changing, starting with a Public Preview.
What’s behind it?
With the new VDI solution for Teams (also referred to as “VDI 2.0”), Microsoft has replaced the existing WebRTC-based optimization with a new media engine called SlimCore, the same engine already powering the native Teams desktop client for Windows. The goal is clear: true feature parity between the native and virtualized Teams client, regardless of the endpoint device.
For Windows endpoints, SlimCore has been generally available since late 2024. Since early 2026, support for macOS endpoints is now in official Public Preview, for AVD and Windows 365 environments.
The official reference: Microsoft 365 Roadmap ID 502524 and the Microsoft Learn documentation for the new VDI solution.
Important: MAU version, not the App Store
There is one key detail here that is easy to miss:
MAU stands for Microsoft AutoUpdate, Microsoft’s update mechanism for macOS apps. The MAU version of the Windows App is obtained directly from Microsoft, not through the App Store. If you have been using the App Store version, you will need to switch to get the new optimization. The minimum required version is Windows App for Mac 11.3.2.
Prerequisites at a glance
| Component | Minimum version |
|---|---|
| Windows App for Mac (MAU version) | 11.3.2 |
| Microsoft Teams in AVD/W365 | 24193.1805.3040.8975 |
Enabling Public Preview: Admin steps
Public Preview is enabled via a Teams Update Policy in the Teams Admin Center, the same mechanism used for all Teams preview features.
... > Settings > About Teams > Early access, enable Public Preview and restart Teams when prompted.
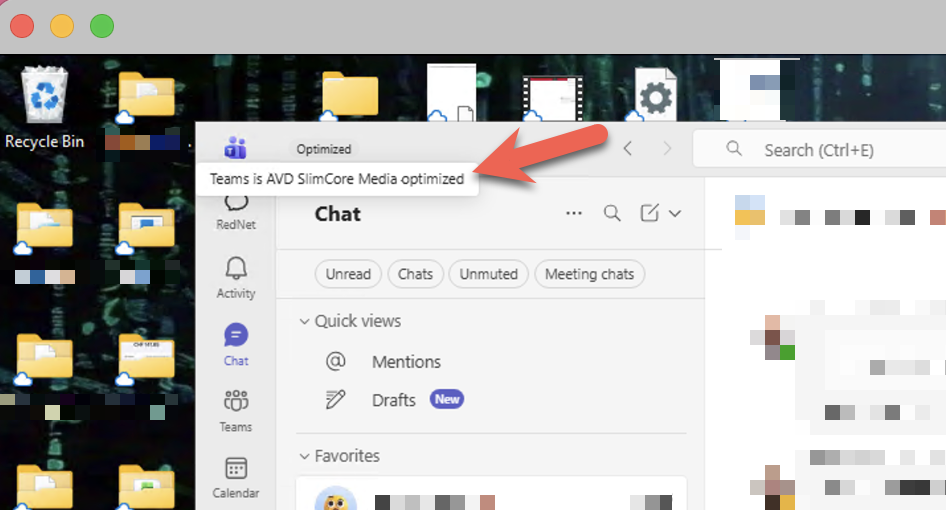
How do I verify the optimization is active?
In the virtualized Teams client, navigate to ... > Settings > About Teams:
AVD SlimCore Media Optimized
New optimization active. All good.
AVD Media Optimized
Legacy WebRTC optimization active. Not yet on SlimCore.
AVD Media not connected
No optimization active.
Newer Teams versions also display a VDI status indicator directly in the top-left corner of the UI, no more digging through settings.
Conclusion
For Mac users in AVD/Windows 365 environments, this is a real step forward. The SlimCore optimization brings features like 1080p video, Gallery View 3×3/7×7, hardware acceleration, and significantly better performance, all things Windows users have known for a while. I’m genuinely pleased to see this finally coming to Mac.
It’s a Public Preview for now, so test it with appropriate expectations. But the direction is right.
Official links
📄 Microsoft Learn: New VDI solution for Teams
🗺️ Microsoft 365 Roadmap: ID 502524
All information in this article is based on publicly available information from Microsoft.
Service Principals vs Secure Clients – Citrix Cloud Gets More Secure
TL;DR
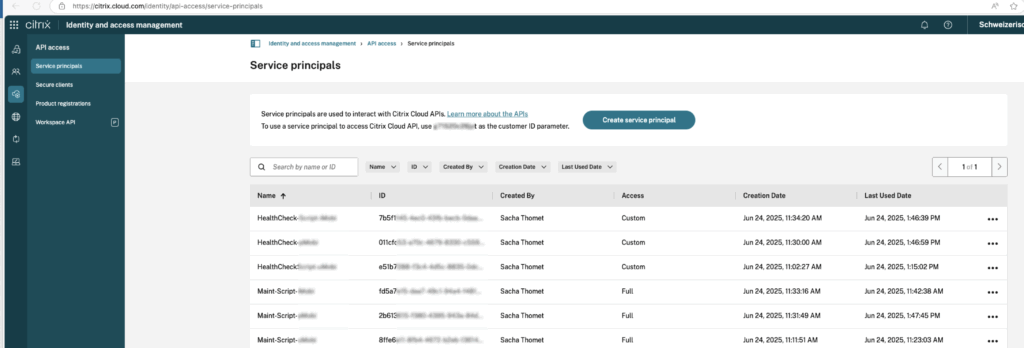
In January 2025, Citrix officially introduced Service Principals for Citrix Cloud as a secure alternative to Secure Clients. They offer time-limited secrets, role-based access control, and detailed audit logging.
Longstanding Concerns – Now Addressed
In my recurring presentation “Benefits and Challenges with Citrix DaaS – Journey of 2 Swiss Citrix Customers to the Citrix Cloud”, I repeatedly raised concerns about the security risks of Secure Clients: non-expiring tokens, lack of permission scoping, and limited logging.
With the introduction of Service Principals, Citrix has finally delivered a solid solution.
Why Service Principals Matter
- Centralized Permission Management: Assign granular, role-based permissions – fully decoupled from the account that created them.
- Expiring Secrets & Rotation: Secrets are time-limited (you can choose the lifetine), and Citrix sends reminders before they expire.
- Improved Audit Logging: API logs now show which Service Principal triggered an action – adding much-needed transparency.
- Smooth Migration Path: Existing Secure Clients can be replaced without major disruption.
What You Should Do Now
- If you’re still using Secure Clients in Citrix Cloud, it’s time to switch to Service Principals:
- Create Service Principals with least-privilege access.
- Configure secret expiration and plan for secret rotation.
- Also migrate automation processes (e.g., Ansible, VM provisioning, etc.) to use Service Principals.
- Leverage official documentation and tools to implement the change.
Useful Citrix Resources
- 🔗 Feature announcement: “Service Principals to replace Secure Clients in Citrix Cloud” (Jan 30, 2025)
- 🔗 Step-by-step guide: “Get started with Citrix Cloud APIs” (May 2025)
Final Thoughts
Citrix Service Principals bring modern security best practices to Citrix Cloud – with scoped access, expiring credentials, and full audit visibility.
I’ve created different SP’s for different scripts and scopes with different persmissions
If you’ve been holding off due to legacy Secure Clients, now is the time to upgrade and future-proof your environment.
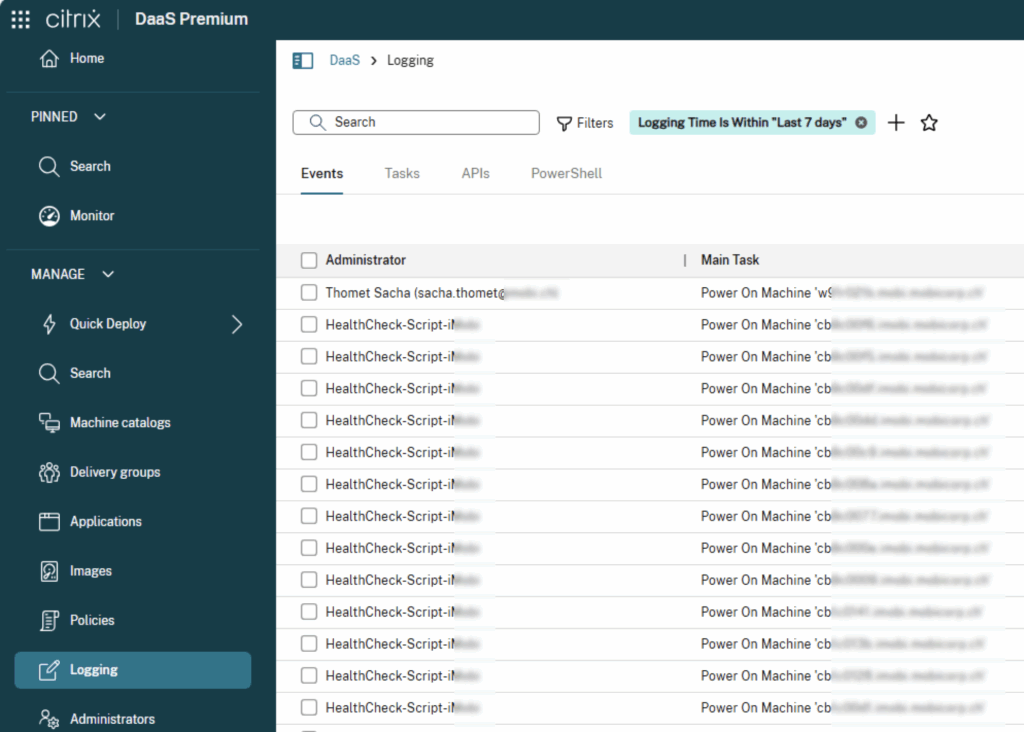
Also in the log you can see which SP is used:
I became a Microsoft MVP – a few thoughts
Today was one of those special moments: the delivery guy brought me the Microsoft MVP trophy – big, heavy, made of real glass. And yes, it looks pretty good on the shelf, right next to the other trophies I’ve collected over the years from the end-user computing world or from my activities as a scuba diving instructor. But this one… this one is special.

Why?
Because it doesn’t just recognize technical excellence. And honestly? I’m sure there are many people out there who are more technically skilled than I am. People with deeper expertise, cleaner code, or more complex architectures.
But I’m visible. I share what I know. I bring people together. I support others – through mentoring, talks, or just by taking the time to write things down when I discover something useful – and also by organizing events and the SwissEUC user group. I post on my blog, on LinkedIn, or on the fast-moving platforms like Twitter and Bluesky (yes, I still call it Twitter, even if it’s now X).
I believe that’s what being an MVP is really about: not knowing everything, but sharing what you do know. Strengthening the community. Enabling connection.
But let’s be clear: I didn’t become an MVP on my own. This recognition also belongs to the people around me – my coworkers, who challenge and inspire me every day. My friends in the community, with whom I organize events, brainstorm ideas, and shape visions. And my family, who supports my activities, encourages me, and gives me the time and space to stay engaged.
I’m grateful – for the recognition from Microsoft, and for the amazing people who’ve been part of the journey so far.
Let’s keep going. Keep sharing. Keep learning. Keep growing.
– Sacha
Why the Windows App for Mac (v11.1.4) is a personal highlight for me
TL;DR: The new Windows App for Mac (Version 11.1.4) introduces two key features that are barely or not at all mentioned in the official release notes, but make a big difference:
1. YubiKey/Passkey support directly inside the AVD session
2. Much improved behavior when resizing across one or multiple monitors
This version finally makes AVD on Mac truly usable for me – an unexpectedly big step forward.
For over two years, I’ve been hoping that Microsoft would bring the Windows App for macOS (the successor to the old Remote Desktop App) up to the level of the Windows version – especially regarding authentication options like FIDO2/YubiKey (WebAuthn).
In the company I work for, we actively use AVD, for example, as virtual development environments. Within our internal network, we rely on secure authentication with YubiKey – which works flawlessly on Windows devices or with Citrix, but not with the Windows App for Mac.
I also addressed this issue directly with Microsoft folks – namely Christiaan Brinkhoff and Sandeep Patnaik – at the Workplace Ninja Summit 2023. I love how at such events you can speak directly with PMs and give instant feedback. But it seemed to me that the macOS version wasn’t exactly a top priority at Microsoft. There was also a Microsoft User Voice for this topic, but since it didn’t receive many votes, it wasn’t given a high priority within Microsoft.
All the more surprising, then, when just a few days ago I stumbled upon the new version 11.1.4 – without any big announcement or fanfare. And suddenly, almost everything that had been missing just worked.
My personal highlights – not found in the release notes:
The official release notes mention some UI and session stability improvements – which is nice, but my real highlights are barely mentioned:
🔐 YubiKey and Passkey support in AVD sessions
A feature I’ve wanted for years: The ability to authenticate directly inside the session using a FIDO2 key, for example in internal portals or apps.
Previously, the Mac system would block the key or not recognize it at all:
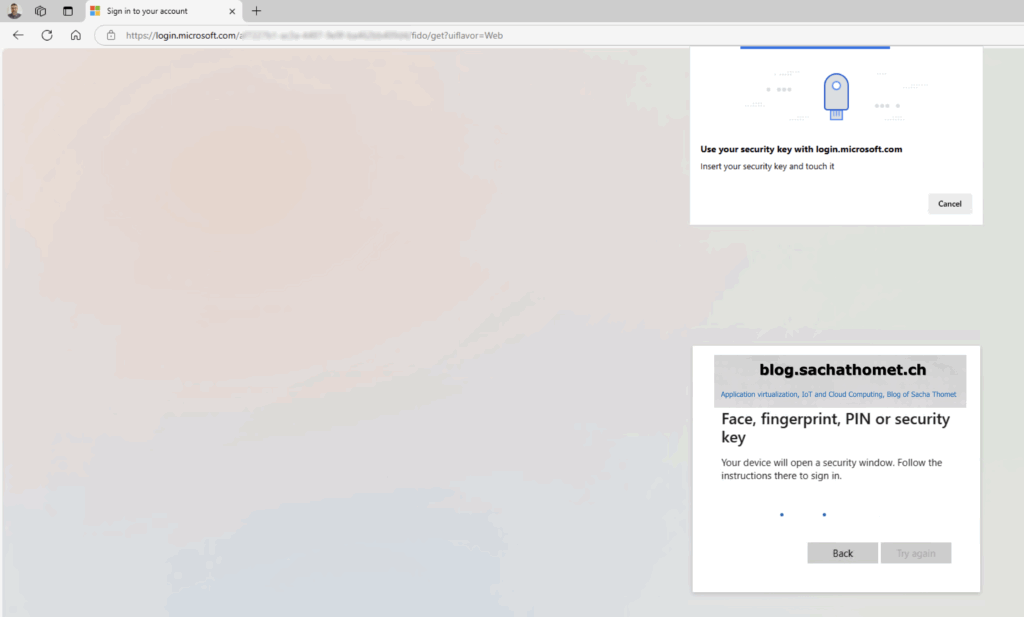
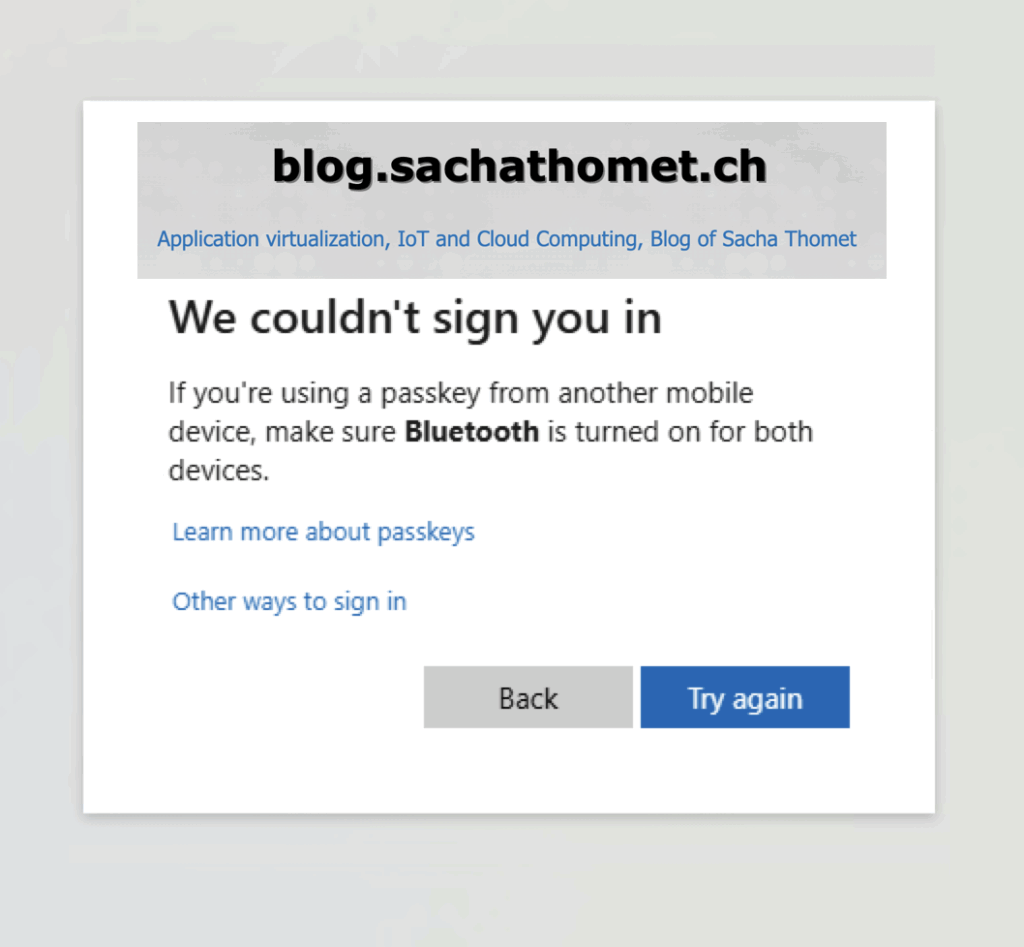
was sadly the result when trying to use the YubiKey before.
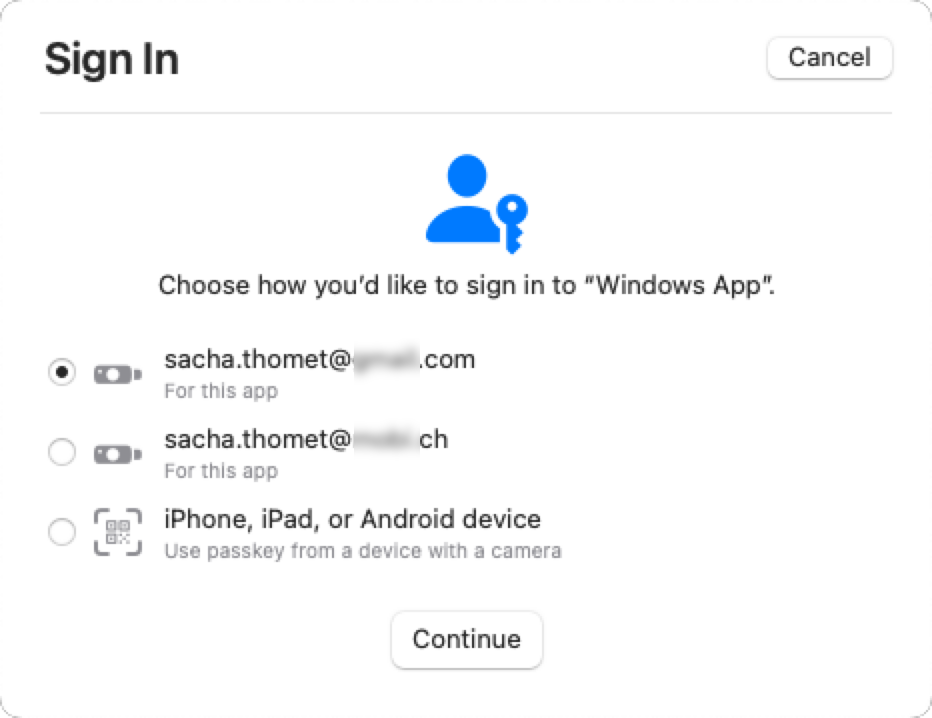
Now it finally works – seamlessly and without hacks, Key Pinpad appears:
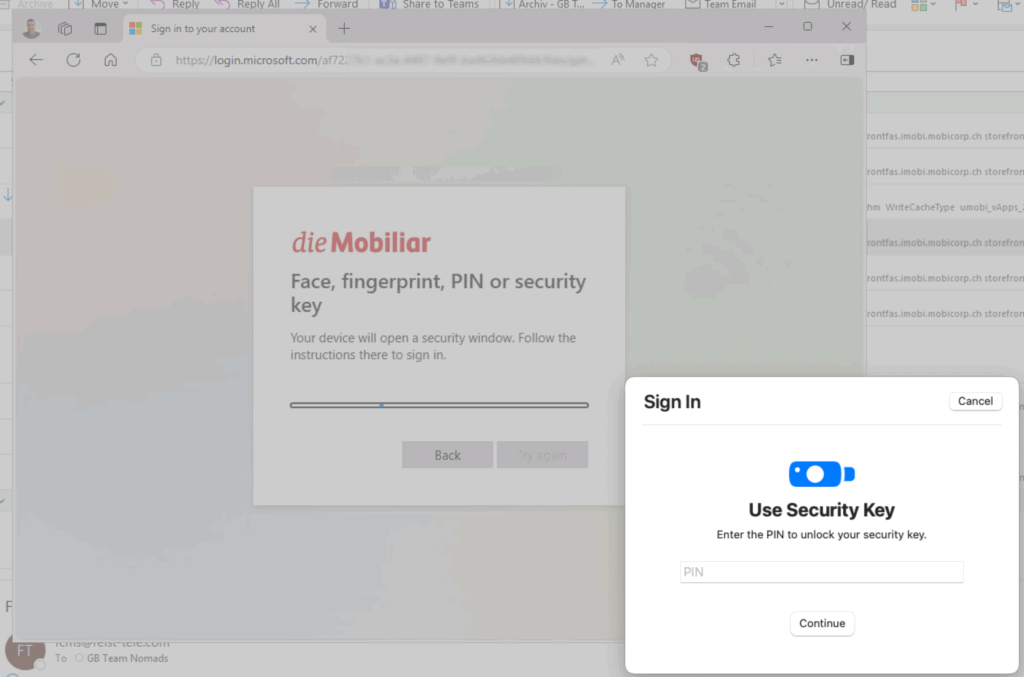
And if you have multiple identities on one Key, even the identity selector appears:
🖥️ Dynamic resizing across multiple monitors
Previously, minimizing a fullscreen session from 2 monitors down to 1 looked like this:
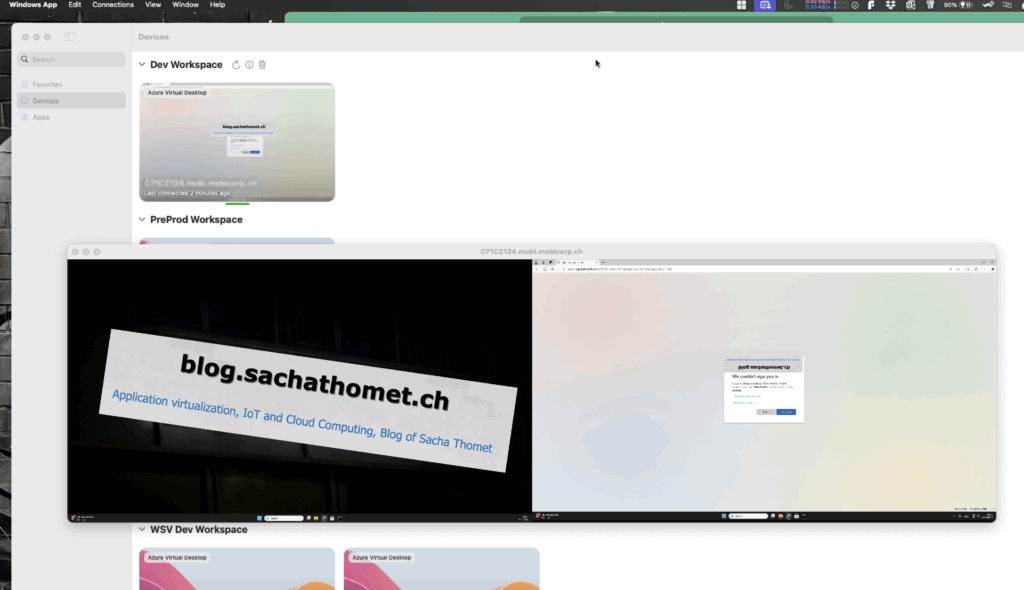
Here’s another subtle but noticeable improvement: The session now adjusts much better when switching between fullscreen and windowed mode, or when working across multiple monitors.
Previously, this often caused incorrect resolutions or frozen layouts – now it just works smoothly.
Who should update? Conclusion
If you’re accessing AVD or Windows 365 from a Mac, this update is absolutely essential. (The update is availible over the Apple AppStore)
While the Windows App for macOS may not yet be a full replacement for Citrix, it’s becoming an increasingly serious alternative.
One more thing … my current opininon
Citrix is still the technological leader – especially when it comes to feature set and protocol flexibility. But it’s also worth asking: do you always need everything Citrix has to offer?
Microsoft has clearly made significant progress recently, particularly in terms of protocol performance and display rendering. With updates like this, the gap is closing rapidly – faster than many might expect.
Just today, I ran a quick comparison using Remote Display Analyzer. I played my employer’s latest promotional video in fullscreen mode on one display and measured data transfer over 15 and 18 seconds respectively. The result? RemoteFX is no longer significantly behind ICA when it comes to data transmission.
Citrix HDX aka ICA: 163.3 MB in 15 sec
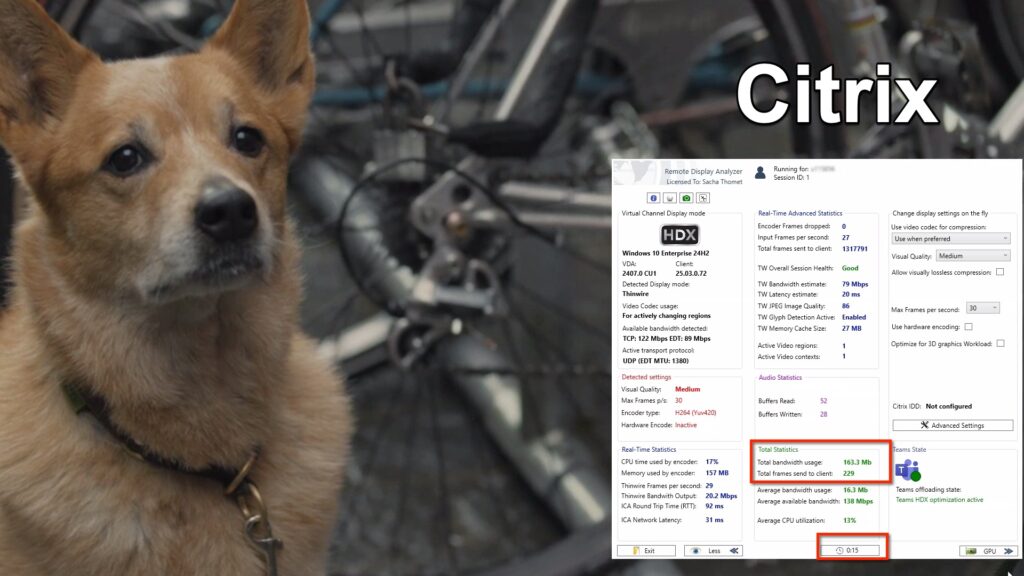
Microsoft RDP RemoteFX: 168.9 MB in 18 sec

Multiple Personal Desktops with Azure Virtual Desktop – A Likely Underrated New AVD Feature
Last week, I was delighted to discover a LinkedIn post by Christiaan Brinkhoff pointing to the blog post “In public preview: Multiple personal desktops with Azure Virtual Desktop.”
In our company, we’ve really missed this feature. We typically follow a “one device strategy,” where each user has exactly one device – either a physical laptop or a virtual desktop (VDI). We’ve been using VDIs for a long time, especially for external partners, test environments, and internal users with special requirements. Until now, we have implemented this On-Premises with VMware as the hypervisor and Citrix as the broker. Providing multiple VDIs per user has never been a technical problem.
Currently, however, we are in the midst of a cloud transformation, and Azure Virtual Desktop (AVD) is the cloud-based VDI solution of our choice. But here, we encountered a limitation: the ability to assign multiple virtual desktops to a single user. This made the announcement of the new feature even more exciting for me, even though it is still in public preview. I do, however, expect that it won’t be long before this feature is generally available.
Why is this a game-changer?
I’m convinced that many companies face similar challenges to ours. For instance, software testing often requires more than one virtual machine (VM). Similarly, robotics VDIs frequently need to access multiple desktops on the same user. Moreover, there are cases of incidents where it is better not to repair the virtual machine but rather to replace it with a new instance based on the “pets vs. cattle” principle. In these scenarios, it can be very useful to temporarily have access to two virtual desktops to extract data or transfer certain configurations from the old VM to the new one.
Previously, the only way to achieve this was through two host pools. The downside was that the user would see two resources, even if they were only permitted to access one of the two VMs. With the new feature, this is no longer an issue. Even when using multiple host pools, the feature ensures that no “ghost resources” are displayed when no resource is available for a user in a host pool.
What’s new and how do you enable it?
As you can see in the image, activating this feature is very simple – you just need to set a flag to enable the functionality:
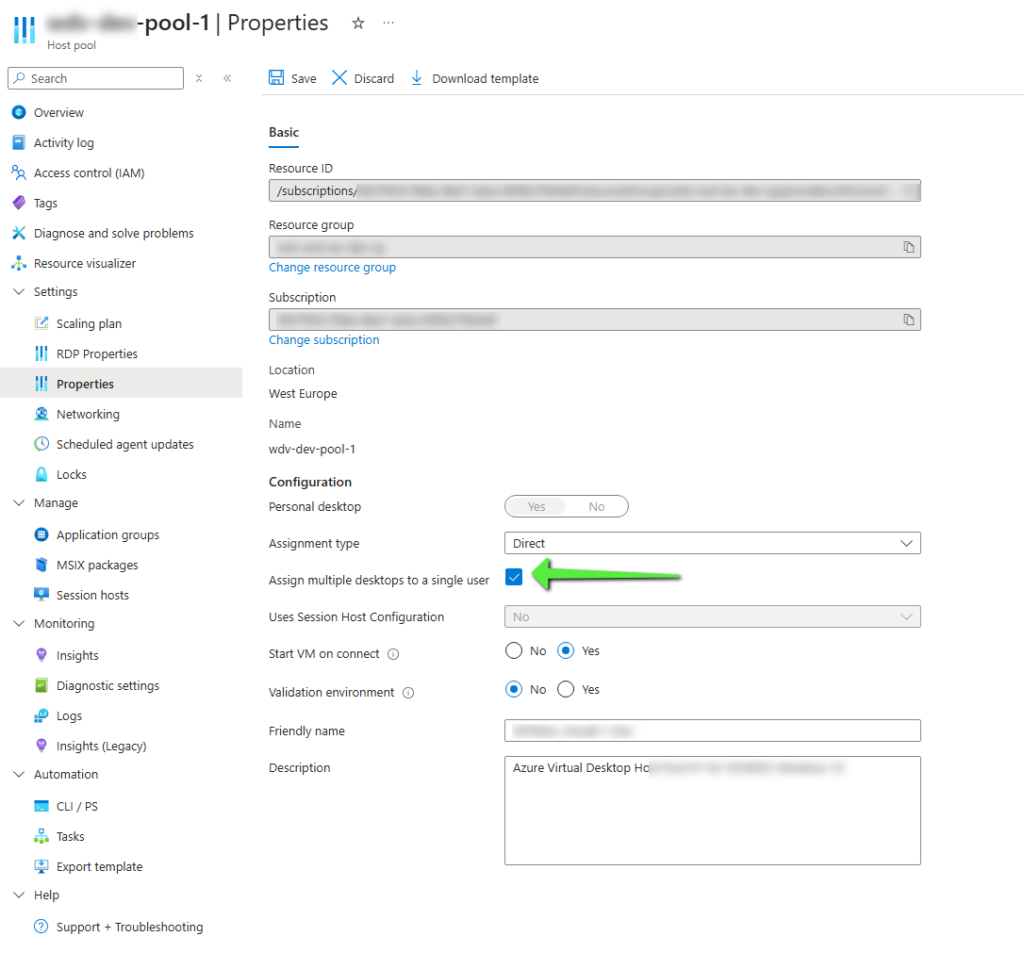
After that, a new field named “Friendly Name” appears in the AVD client to help users differentiate between the virtual machines:
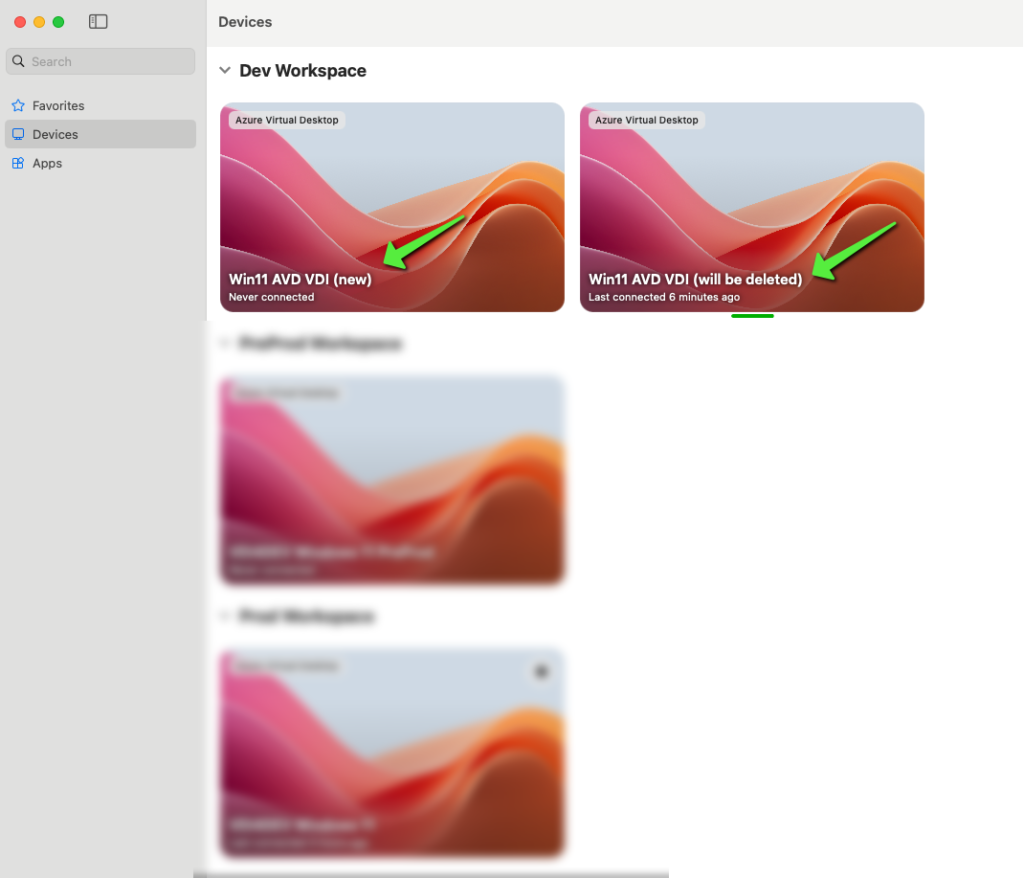
Limitations of the feature
Currently, this feature only applies to AVD Single-Session machines. It does not work with Multi-Session deployments or Windows 365. It’s unclear whether or when this feature will be made available for Multi-Session environments, but in my opinion the need is more fore SingleSession VDIs.
Conclusion
This new AVD feature is a real step forward for companies that need multiple desktops per user, whether for testing, troubleshooting, or special requirements. I am excited to see how this feature evolves and when it becomes generally available. It will certainly help many companies make their VDI environments more flexible and user-friendly.
What’s your opinion? Is this feature another step toward feature parity with existing virtual desktop solutions? What would be your next desired feature? Let me know in the comments.
From OnPremises to Cloud – what should it be? A quickstart to the Azure VDIs
Currently, more and more companies are facing the question of whether to continue offering their VDI on‑premises traditionally or whether it should be provided from the cloud in the future.
The EUC world is in transition, and today there are far more serious alternatives than just one or two big, established manufacturers. Or maybe that’s just my personal opinion after stepping out of my bubble a little – but I think there are new needs, and the market is now trying to address them.
I have been a “Citrix tech evangelist” for years, and I am still absolutely convinced of their technology. For me, it’s clear that Citrix has developed the most powerful application and desktop virtualization technologies. However, the competition is catching up, and it doesn’t have to be the ultimate solution for every customer. The company I work for is increasingly focusing on Microsoft and has been pursuing a cloud strategy for years.
It follows naturally that the option to replace on-premises VDIs with a Microsoft Azure VDI solution must be considered.

Some readers of this page may have had the chance in the last two years to hear the presentation by Fabian Tschanz, Stefan Moser, and myself at one of the events (e.g., at the Workplace Ninja Summit or at E2EVC) – they will know that we already ran a project for our developers using Microsoft AVD Single Session as a developer VDI on “greenfield” sites.
Now, things are easy when you start on a greenfield site; however, replacing existing systems becomes difficult due to existing and sometimes unnamed requirements. Sometimes a solution is built for one purpose and then used for something else – something the platform developers didn’t foresee – so it gets lost during migration. So, requirements engineering must be done again here.
Next, we want to cover the following use cases:
- Dedicated VDI for power users with specific needs (usually without company devices) and
- Users of pooled VDIs, who use the VDI occasionally and may also have a company device.
Microsoft offers many solutions, and new variations are still being introduced. So, what is the right choice?
Windows 365? Microsoft Azure Virtual Desktop? And if that’s not enough – there’s also Windows 365 Frontline and/or AVD Multi‑Session. And what is Windows 365 Frontline in Shared Mode?
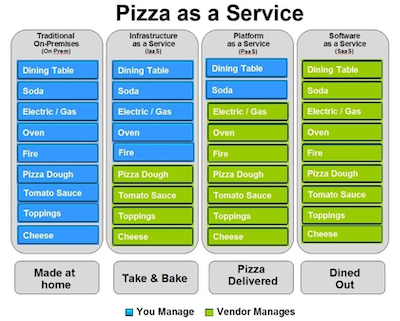
So, let me try to break this down a bit. When I had to explain On‑Prem, IaaS, PaaS, and SaaS to someone, the pizza model (see image here) helped me, which Albert Barron, Global Principal Architect, Financial Services at Google, explained in a 2014 LinkedIn post.
I wouldn’t claim to be as clever and good at explaining things as Barron, but I’ll try to break down Microsoft Azure VDIs – all the ones mentioned above – into different mixtures of PaaS and SaaS.
Windows 365 Cloud PC
- Fully persistent cloud PC for each user
- Fixed resource allocation (dedicated VM)
- Integrated with Microsoft Endpoint Manager (Intune) for management
- Easy setup without complex infrastructure
🍕In the pizza model, I’d say this is like dining out in a restaurant that always has a place for me – my name is on my dedicated table. I can choose pizzas from the menu in defined sizes. If I provide a recipe, this pizza will be topped and baked according to my wishes.
Windows 365 Frontline Dedicated
- Specifically designed for shift workers or shared usage
- Each user has a dedicated VM that’s only used during working hours
- Licensing based on concurrent usage (not per user)
- Automatic shutdown outside of shift times to save costs
🍕In the pizza model, I’d say this is like dining out in a restaurant where multiple parties share a table alternately – The table is used by three different parties in one day. I can choose pizzas from the menu in defined large sizes. If I provide a recipe, this pizza will be topped and baked according to my wishes.
Windows 365 Frontline Shared
- Multiple users share the same cloud PC
- Specifically for environments with shared workspaces (e.g., call centers)
- Cost-effective usage since no dedicated machine per user is required
- Resources are dynamically allocated
🍕In the pizza model, I’d say this is like dining out in a restaurant where multiple parties share a table alternately – the table is used by three different parties in one day. All parties must eat the same pizza in the same large size. I can choose pizzas from the menu in two defined large sizes. If I provide a recipe, this pizza will be topped and baked according to my wishes.
AVD (Azure Virtual Desktop) Single Session
- Each user has their own VM (similar to Windows 365, but more flexible)
- Support for different VM SKUs (custom performance)
- Management via Azure Resource Manager, not Intune
- Licensing via existing Microsoft 365 licenses or separate Windows licenses
🍕In the pizza model, I’d say this is like dining out in a restaurant that always has space for me – I can decide how the table is set and how big it should be. With pizza, I’m more flexible: it doesn’t have to be round, I can also make it square. If I make a mistake, the pizza gets extremely expensive and I can’t finish it – or it’s so small that I’m still hungry. I can customize the venue and the tables.
AVD (Azure Virtual Desktop) Multi Session
- Multiple users share a single VM (Windows 10/11 Multi Session)
- Ideal for companies with many simultaneous users (e.g., remote workplaces)
- Resources are flexibly shared among users
- More cost-effective than Single Session, as fewer VMs are needed
🍕 Similar to AVD Single Session, but I can let multiple people eat from a single pizza – this way I can efficiently make one pizza. The pizzaiolo only needs to serve one table because we need only one table, but eight people will be full. However, all eight must eat the same type of pizza. I can customize the venue and the tables.
So, what’s the right choice? Well, it really depends on the needs – there’s no wrong solution, maybe the solution just doesn’t fit the problem, aka challenge or use case.
In the coming weeks and months, I will likely be exploring the more flexible solutions with Azure Virtual Desktop in the Single Session and Multi Session variants, and I’m sure I will still face some decisions here…
The CTP Program Has Ended – A Personal Retrospective
Now it’s official, and I believe this post doesn’t break any NDA. Those of you who have followed my IT career a bit know that I’ve been a “Citrix Evangelist” for many years. It all started in 2001 when I made my career switch into IT at the SBB Service Desk. That was the first time I came into contact with Citrix products, and over the years, this connection deepened. Especially in 2013, when I moved from the service provider T-Systems to the customer side, I had the opportunity to become even more active in the Citrix community.
A major milestone was winning the Geekovation Award in May 2015 at Citrix Synergy in Orlando – a moment that introduced me to the Citrix Technology Professionals (CTPs). Meeting these brilliant minds was inspiring. During a breakfast at the E2EVC conference in Lisbon, I had a defining conversation with Perrine, who encouraged me to apply for the CTP program. Although I had little faith in my chances, I took the leap – and to my surprise, since 2016, I was part of this exclusive network. The first CTP meeting in Las Vegas was, and I rarely use this word, simply “mind-blowing”!
My employer, Mobiliar, always supported me in fulfilling this role, particularly my direct Citrix colleagues, team leaders, and people leads.
Unfortunately, the direction of the Citrix community has changed. Last year, the CUGC was discontinued, and now the CTP program has also come to an end, as I learned last week. More details can be found here: https://www.theregister.com/2025/01/27/citrix_axes_its_technology_professional

Thanks to my role as the leader of the Swiss CUGC (Citrix User Group Community), I was able to bring the customers’ voices into the development of Citrix products and build a bridge – a contribution I’m proud of.
I am deeply grateful to Citrix – but above all, to the people I was fortunate to meet through the CTP program. Friendships that would never have formed without this program will endure. The virtualization and end-user computing market continues to evolve – hopefully for the benefit of customers. Fresh ideas and new approaches will drive innovation.
It has been an incredible journey, and I look back on this time with gratitude.
The market for virtualization and end-user computing continues to evolve—hopefully to the benefit of customers. Fresh ideas and new approaches are driving innovation. I remain actively engaged in the community because, after all, a little refresh now and then does me good as well.
At the same time, I am expanding my horizons and increasingly working with other technologies. With the launch of SwissEUC in 2024, together with Stefan Beckmann and René Bigler, I already took a step towards vendor neutrality.
Currently, my focus is on Microsoft’s virtualization and EUC products, particularly Azure Virtual Desktop, Windows 365, and its various “flavors”—whether Single Session vs. Multi Session or the Frontline model of Windows 365.
Exciting times ahead!
Tokenbased Citrix VDA registration
and how to combine the Microsoft AVD world easily with Citrix DaaS …
Over the past few months, Citrix has made significant investments to make the Virtual Desktop Agents (VDAs) independent of Windows domains. This was particularly important for Linux and Mac systems, and for some time now, it has been possible to provision non-domain-joined VDIs in Azure using Citrix tools. New in version 2407, available for the first time as a Tech Preview, is the ability to integrate Windows machines provisioned through other methods using a token, without requiring a domain, Delivery Controller, or Cloud Connector.
During the VDA installation, instead of specifying a Delivery Controller (DDC), the token can be directly provided:
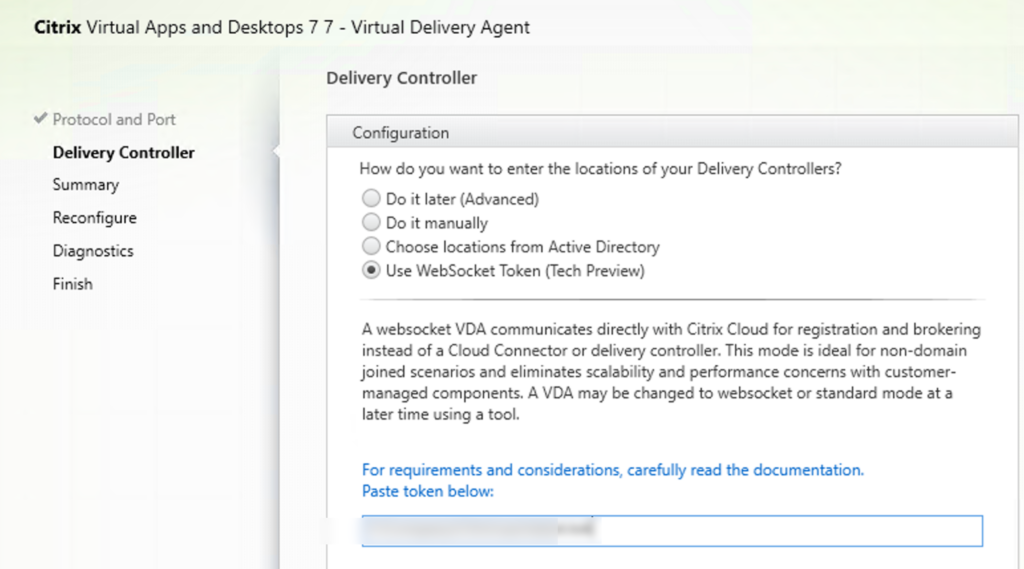
(Important: The token itself, not the path to the token file, must be specified. This will maybe in future changed to provide a token File).
Instructions from Citrix: https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/install-configure/install-vdas.html#step-7-delivery-controller-addresses
The token must be generated first in the Citrix DaaS Console on the appropriate machine catalog where the VDA is to be integrated, via right-click:
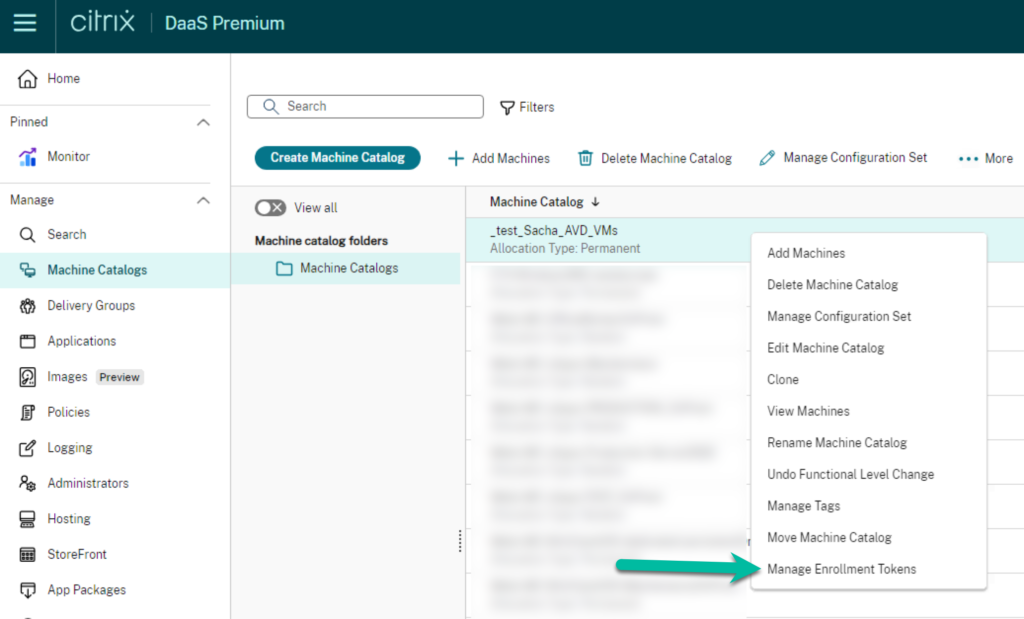
It has to be a machine catalog with the Provisioning Method on the Setting Manual.
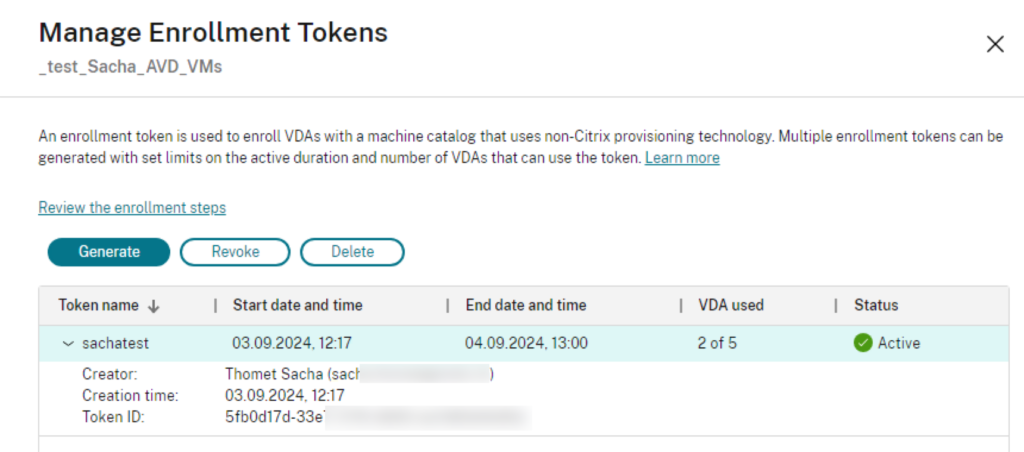
A single token can be used to deploy up to 100 VDAs, and the token is valid for a maximum of 14 days.
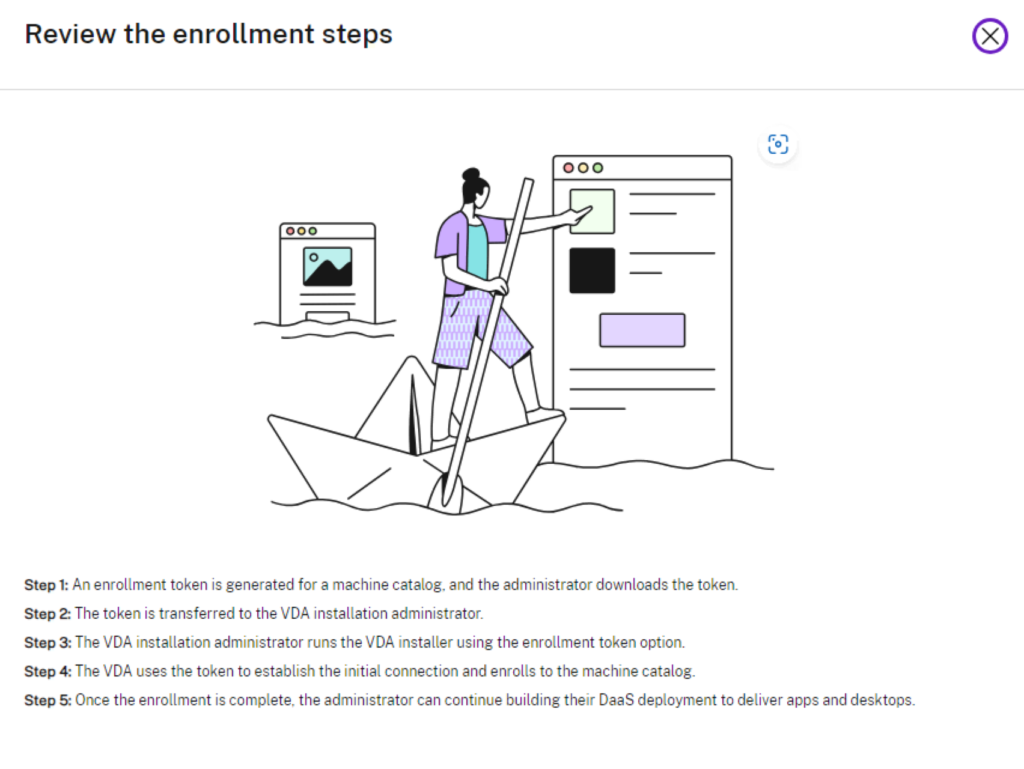
The installation steps are also described in the “Review the enrollment steps” section.
I used this new feature to integrate Azure AVD VMs created via pipeline into Citrix, which I had previously used through AVD. Now, I essentially have a VDI that I can broker and connect to traditionally via Microsoft, but also through Citrix. You may ask yourself why someone want to have the whole Citrix brokering stuff, but not using the Citrix provisioning method for Azure (MCS), this can have different reason, possibly because someone want to use an automated IaaS pipeline with bicep and have control over the provisioning / building of the infrastructure, or other obstacles to not using the Citrix techniques to build VMs. I can’t say more here, I just see a way to make things different and gain more control but still use the advantage of the Citrix techniques in brokering and the ICA protocol.
Since my machines are only in Azure AD, it is important that I configured the delivery group to set the LogonType to AzureAD. I accomplished this with the command:
Set-BrokerDesktopGroup <DeliveryGroupName> -MachineLogonType AzureAD
Additionally, if I still want to access the machine without Citrix, I need to add my user to the Direct Connection Access group. Otherwise, when connecting without Citrix, I will receive the following error:
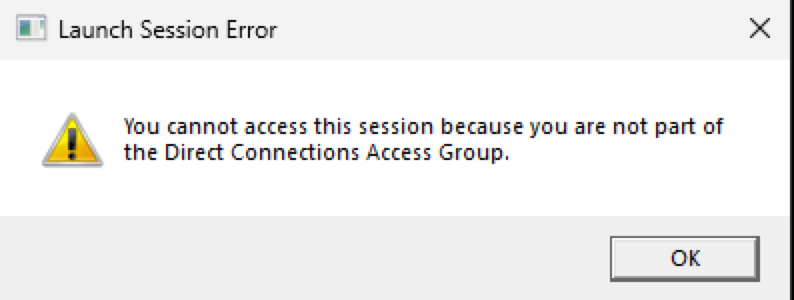
These are my first experiences with the new token-based VDA rollout. Of course later these steps must be automated for a business environment when using the token, whereas in my hands-on experiment, everything was done manually through the graphical interface. If you are experimenting with this, please keep in mind that’s a TechPreview and not yet GA.
Why I love my Meta Rayban
I was at an IT conference in Barcelona last week. Not only did I learn a lot, reconnect with old friends, and meet new people, but I also brought back inspiration and good memories. Additionally, I had the chance to test the Meta Ray-Ban, which is not yet available in Switzerland, thanks to my Danish friend Thomas Poppelgaard. At the airport Ray-Ban store, I got myself a pair of Ray-Ban Meta glasses, and I must say, I am fascinated. Moreover, I made my first extended vlog, which is available in “Swiss English” and Bernese German:
And Swiss German:


Recent Comments